This Is How Hackers Are Fooling You & Your Business
By Prethiba Esvary, Marketing and Communications Executive, Lava Protocols
Last year, approximately 1.5 million patients’ non-medical records were stolen from the SingHealth (a group of healthcare institutions in Singapore) database. To add to that, about 160,000 patient’s medical records — including that of the current Singapore Prime Minister Lee Hsien Loong’s — were accessed illegally. This is one example of a huge case of data breach.
Do you remember the CIMB Clicks password issue that took place last year? People claimed that they could log in despite adding a few invalid characters after the required 8-character password. Then there was the issue of fraudulent debit card transactions. Several CIMB customers complained that there were unauthorized Paypal transactions made via their debit cards.
Our question is how can hackers get access to what you would think are high-security systems? Was this a human error or simply due to the absence of a robust security system?
The Facts
A study by Frost & Sullivan revealed that Malaysia is looking at a possible loss of US$12.2 billion (approx. RM50.7billion) due to cybersecurity attacks.
In a press conference in July last year, Frost & Sullivan Asia Pacific Marketing VP Saipan Agarwal said, “Cybersecurity attacks have resulted in job losses across different functions in three out of five organizations that have experienced cyber incidents over the last 12 months.”
In reference to the SingHealth database hack, associate director of security services provider LGMS CK Fow said that most of the time, cybersecurity attacks are due to human error and they usually come from within the organization.
The problem is that organizations tend to place more importance on back-end security (servers, firewalls, intrusion prevention systems), he added.
“They may forget the most important part, which is the front-end security, such as end-user computers,” he said.
With regards to the CIMB Clicks password issue, the bank released a statement on Dec 17 last year saying they have beefed up their security by accommodating passwords of 8 to 20 characters in length and by adding reCaptcha. As to the fraudulent transactions, CIMB confirmed in a public FAQ released on the same date that this matter was separate from CIMB Clicks. A question raised was why wasn’t there an OTP (one-time password) issued to customers to warn them of suspicious transactions?
According to CIMB, “The use of OTP is a policy adopted by e-commerce site owners. Whilst online transactions on Malaysian websites require an OTP (called 3D authentication), many international websites such as Facebook or PayPal do not require an OTP (called Non-3D transactions)”.
How can consumers protect themselves in that case? Go to the solutions section of this article.
A Cause for Concern for Your Business
Believe it or not, hackers are now more interested in targeting businesses rather than individual consumers, the 2018 Phishing Trends and Intelligence (PTI) Report stated.
What are phishing attacks? It is when a hacker masks their true identity behind a trusted entity in an attempt to steal personal and sensitive data from users such as login credentials and debit/ credit card details. They do this by tricking users to open emails and text messages and to click on malicious links. This “can lead to the installation of malware, the freezing of the system as part of a ransomware attack or the revealing of sensitive information”.
The report also said that hackers are impersonating email service providers and Software as a Service (SaaS) platforms in an attempt to steal corporate data and access their systems. Once a single user has accidentally given access to his/ her account, hackers are able to access all sorts of data from the organization. In fact, they can use this to send malicious emails to other employees. Now that there is the single sign-on function, hackers can also use that to access all the other SaaS services.
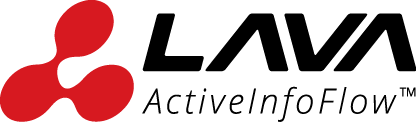
Take a look at this email:
This mage is taken from www.phishing.org and intended for illustration purposes only.
When we get security warning emails from e-commerce sites or email service providers we have accounts with, naturally, we would assume it is from a trusted source. Hackers take this to another level by mimicking these emails (down to the logo, font, sender’s email, and colors), just to get you to click on a malicious link.
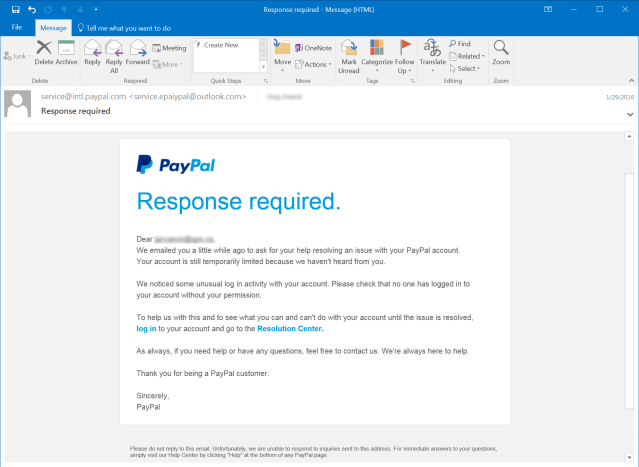
In this case, you should hover over the link to ensure it is from a legitimates source BEFORE clicking on it. You’ll be able to see the source at the bottom left of your screen.
This is a screenshot taken from the author’s inbox and is purely for illustration purposes.
You would also think that sites that contain HTTPS are trusted as it encrypts your communication. Apparently, that’s not the case anymore. Hackers have become smarter and are exploiting this for their own benefit. The same report stated that “by the end of 2017, nearly one-third of all phishing sites were hosted on HTTPS infrastructure, compared to just five percent at the end of 2016…”
I can go on and on.
Read more: Four Phishing Attack Trends To Look Out For In 2019
The Solution
1. Two-step verification method on Google
This means that every time you sign into your Google account, you’ll need to put a password and verification code. The code is sent via text message, voice call, or Google’s mobile app. This way, even if hackers somehow got a hold of your password, they can’t log in.
Of course, you have the option of not going through this two-step process again and again if you’re on the same computer/ device. But the moment you yourself sign in from another device, the two-step verification is needed.
2. Strengthen your CRM platform security
If you’re using a CRM platform such as Salesforce, there are several security measures you can take. One is the two-factor authentication approach. You can set this up for every user’s login, log in through API (for developers and client applications), and also for access to particular features such as reports and apps. Users would have to either download a Salesforce/ Google mobile authenticator app (to receive push notifications or OTPs via the app) or use a U2F security key as the second-factor authentication.
The second security measure you can take is to include IP range restrictions. This means you will be restricting users to log in only from your company network or a VPN (virtual private network).
Last but not least, it would be good to add spam filters and malware protection to your system.
3. Check the website domain
Since hackers are now mimicking other ‘https’ sites, what you can do is to check the domain. Say you have an account on amazon.com. Hackers can easily create a website that looks exactly like amazon.com. But if you look closely, you may see that the domain is actually amaz0n.com. That’s because no two users can purchase/ have the same domain.
You can also look at the following:
- Company address and phone number – If these aren’t available, then something is not right.
- Prices – If they are incredibly low, something is fishy.
- Return policy – Any reputable site would have a section on product returns and shipment.
- Privacy policy – A legitimate site would have details on how they are using your data and how they are safeguarding it.
4. Check the security settings on e-commerce sites
If you’re a Paypal user, you ought to know that there is actually the option to enable the ‘Paypal security key’, which acts as a second authentication factor. So, in addition to keying in your password, you would have to key in a security code/ OTP which will be sent to you via SMS.
5. Use a foolproof password
It’s understandable why people would use their IC/ birthdays as their go-to password, and that too for EVERY account. It’s easy to remember! But say you lost your entire wallet one day/ someone breaks into your home and gets a hold of your bank cards and identification card. They can easily transfer out all the money you have in all your bank accounts.
Second thing is, ensure that all your passwords have a combination of numbers, letters, and special characters. That way, it’ll make it impossible for hackers to guess what your password is.
In a Nutshell
Both human error and a lack of multi-layer security on your front and back-end systems are the main cause for all of these cyber attacks. With regards to the former, it is crucial that your organization takes measures to prevent employees from ‘copying databases’ or ‘sensitive data’ and to also put in a place something to detect if and when they have done so. For the latter, implementing the right security measures is key. Therefore, speaking to the right IT or cloud service provider would be a good place to start. Lava Protocols has worked with numerous clients over the past decade with their cloud solution implementation and also data security.
If you’d like to speak to one of our consultants about how you can beef up your security measures, email us at asklava@lavaprotocols.com or call us at +603 7885 9720.
A few weeks ago, one of our employees nearly lost all of her savings because of a scam. Read the full story here.
————–
Lava Protocols is a cloud service provider in Malaysia. We are also an authorised Salesforce Partner and we possess more than a decade of experience in CRM solutions for sales, service, and marketing. We pride ourselves in not just being a CRM partner but also understanding the needs of our customers and taking their business to the next level.